software development
What Can Men Do?
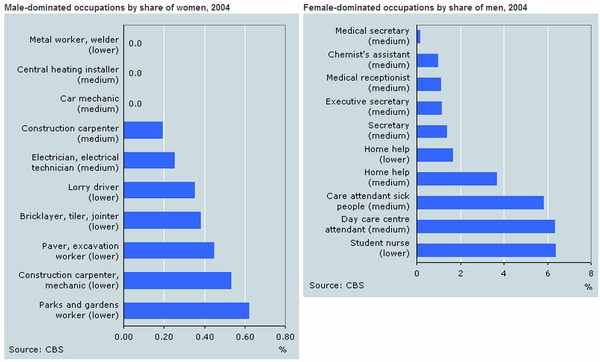
(The title references Shanley Kane’s post by the same name. This post represents my views on what men can do.) It’s no secret that programming is an incredibly male dominated field. * Figures vary, but somewhere from 20% to 29% of currently working programmers are female. * Less than 12%