Localhost HTTP Debugging with Fiddler
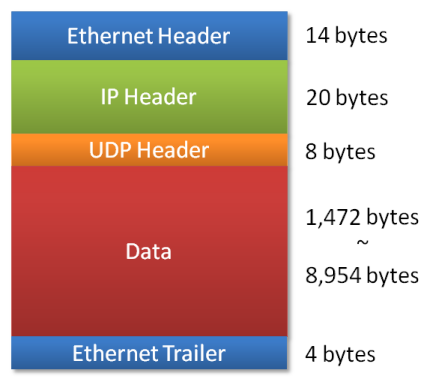
I’ve had great success using ethernet sniffers (such as Etherdetect, or Ethereal) to troubleshoot communication problems. Installing a sniffer, even after installing the required WinPcap packet capture library, doesn’t require a reboot. I frequently use sniffers to troubleshoot servers and desktops alike. Ethernet sniffers should be a standard tool in your development troubleshooting toolkit, too.
However, Windows ethernet sniffers do have one significant limitation: they can’t sniff localhost traffic. Localhost packets don’t pass through the regular network stack, so they’re invisible to an ethernet sniffer.
What’s a poor developer to do? The only recourse is a local HTTP proxy, such as Fiddler:
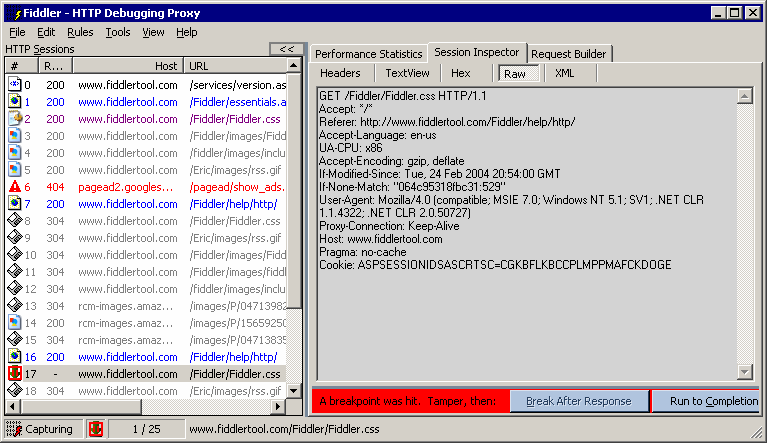
Fiddler has some special integration with IE that makes it particularly easy to use, but it can be used with Firefox as well.
I had some erratic results under IE7, but Fiddler basically works as advertised. There’s tons of supporting documentation on how to use it, including two MSDN articles. I’m using Fiddler as a localhost sniffer that’s limited to the HTTP protocol, but it does have some capabilities beyond what you’d see in a sniffer. For example, with Fiddler you can set breakpoints and tamper with the HTTP data before it is sent or received.
On the whole, I’d prefer to stick with a sniffer for localhost debugging. But a HTTP proxy like Fiddler is a reasonable workaround.